As I was leaving Cleveland, there was a great deal of activity around the gate next to mine. There were photographers, people with clipboards, and United branded polo shirt wearers. They were moving through the people lined up to board the plane, and that was when I noticed something different. The usual boarding signage for groups 1 through 5 was missing. In its place was a single sign. One side had a large "A," and the other side had a large "B."
So me being the inquisitive soul that I am, I approached on the polo shirt wearing, laptop holding individuals and asked what was up. Apparently United has been testing multiple boarding procedures over the last couple months to find something that their customers will ultimately prefer with emphasis on satisfying their elite customers.
We had quite an interesting discussion during which he mentioned many things that I found baffling about elite members, of which I am one. Many of the things he mentioned definitely didn't ring true for me, but apparently were typical of most passengers. Interestingly, most of these conclusions were derived from a series of questions that were not direct. They were "emotional" questions such as, "how does it make you feel when you see everyone lined up," and "do you feel less valued when disabled passengers, military members, and families with children are allowed to board before you." There were many more questions that he mentioned, but you get the idea. I will be very interested to see if boarding procedures change in the coming months, and in what way they change.
For me, the only thing I care about is having a place for my rollaboard. Honestly, if they guaranteed me a place for my bag(s), I wouldn't line up until my group was called like they request, but never happens. And I would check my bag if they would get it to me in a timely manner, and ensure that it made it to my final destination. That is unless I'm flying Southwest, in which case getting in line early is practically a must because people don't know that 34 comes before 35.
The World According to Rob
An adventurous stroll into the mind and travel of Rob.
Where I've Been
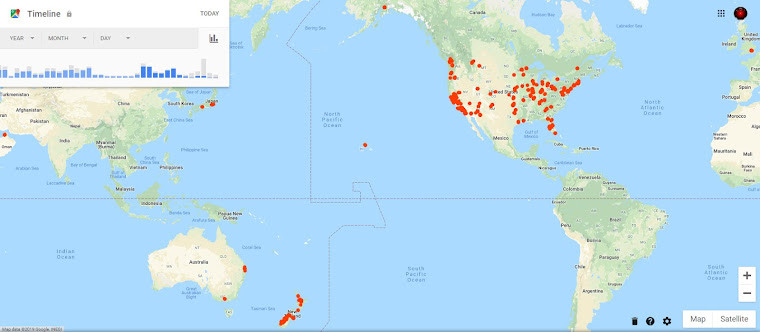
Where I've Been
Friday, September 8, 2017
Wednesday, September 6, 2017
The Great Lakes Are Truly Great
When one looks at a map of the US and sees the little mitten shaped state of Michigan and those bodies of water around it, one likely doesn't understand just how "great" the great lakes are. I'm speaking of their size. We know the land is massive because we recognize the distances of travel between those cities, but at least for me, I have a tendency to diminish the size of bodies of water.
As I was flying into Chicago (top three pictures above) a few weeks ago and then flying home from Cleveland (bottom four pictures above), I was really struck by how big the lakes are. When you look at a city the size of Chicago from the air, and then compare that to Lake Michigan, it really puts it into perspective. Even from 10,000 miles above the Earth you can't see the other side of the lake. And then I remember going to Duluth (pictures below) two years ago, and visiting the maritime museum and read about all the tankers that have sunk in Lake Superior and how deep it is, I realize again that the lakes are truly great in size.
As I was flying into Chicago (top three pictures above) a few weeks ago and then flying home from Cleveland (bottom four pictures above), I was really struck by how big the lakes are. When you look at a city the size of Chicago from the air, and then compare that to Lake Michigan, it really puts it into perspective. Even from 10,000 miles above the Earth you can't see the other side of the lake. And then I remember going to Duluth (pictures below) two years ago, and visiting the maritime museum and read about all the tankers that have sunk in Lake Superior and how deep it is, I realize again that the lakes are truly great in size.
Monday, September 4, 2017
How To Be A GM
I'm deviating from my blog topic of travel to discuss something that came up today when I was talking to my daughter--how to be a GM. After you read this, I would be greatly interested in your input as a GM and/or player, whether you agree or disagree, and what suggestions you would add to help someone be the best GM. At the very end of this entry, I'll provide a great video that I think epitomizes what a game should be like, and a link to a great site for learning how to be a GM and improving your skills.
I've been playing RPGs since my first foray into AD&D in 1980. A childhood friend of mine and his brother bought the three core books and we decided to give it a go. It was relatively easy to become a DM back then--buy a module (a pre-written adventure), read it, and then take the players along for a ride through the module. The module had all the text that described the scene, had the monsters that would be encountered during said adventure, and the treasure that would be doled out once the monsters were slain. And as young kids, we didn't have all the weight of reality sitting on our shoulders. There was little effort required to suspend disbelief. We just got in to the story and went along for the ride. We joked, we ate, we socialized. It was all about improving our characters to become masters of the world, and for the GM it was all about telling the story and finally sharing the secrets and surprises that the players had yet to uncover. For everyone it was about hanging with friends, socializing, and building memories that would be shared for decades. Unfortunately, so much of that has been lost over the last couple decades, and gaming has morphed into a "me, the GM, versus you, the players." This is not conducive to shared fun or fond memories. We've lost sight of the core of gaming, acceptance of fantasy, and especially what a GM's job is.
Socializing, that's the core of gaming. If you can't enjoy hanging out as a group just talking, you probably shouldn't be gaming together. This is the first key point, and so critical to gaming in general. I've played with many groups over the years, both face-to-face and online, and the majority of those groups were not fun to be a part of. It could have been something minor like one of the players just constantly cracking unfunny jokes, something a bit more serious like favoritism among the established friends, to something pretty major such as constant arguing about everything that everyone was doing wrong. I saw it from GMs as well as players. Any injection of poison into the group will result in the dissolving of the group, or at the very least splintering, as irritated players leave the group. Sadly, this poison is almost always the fault of the GM, in the majority of the groups that I joined and then quickly left. (Note: I did not leave all the groups because of that, some I simply couldn't play with due to real life issues getting in the way, especially as I got older, so don't assume a player's departure is do to "poison." Communication is critical here.) As I just mentioned, communication is critical in any group. Everyone needs to be a respected member of the group and treated as an equal. If the group cannot communicate and be honest and open with one another that tends to indicate an underlying problem and the group should either work on fixing it, or breaking up before feelings are really hurt. This is one of the first jobs of the GM--communication. Not just taking the group on the adventure, but also making sure that everyone is treated fairly and equally. Every player should be given an opportunity to give input, and to make mistakes. If a player makes a mistake, don't ridicule the player - a little friendly ribbing is fine, but make it and keep it friendly. The GM is telling a story that is typically only faintly based in reality, after all who wants to play the game commuting to work and doing business after a week of really doing just that. Games are meant to be fantastic, fun, and frivolous.
Fantasy, not swords and sorcery, but the opposite of reality, is what the gaming worlds are set in regardless of the genre. It could be a gritty realistic mission set in modern day, trying to stop some evil corporation from controlling the minds of the populace, but it is still fantasy, and should be treated as such. I feel like the older we get the more we lose sight of the ability to suspend disbelief and we keep demanding more and more realism in our games, and I think this is a very wrong approach to take. Sure, you can go for a high level of reality, but if the players aren't larger than life heroes capable of extraordinary feats, what's the point? One of my favorite systems in my teen years was Aftermath, a game set in a post-apocalyptic world. The system is incredibly crunchy (high level of realism), and characters can die a million ways to Tuesday, but ultimately it was still fantasy. There were still elements of the game that were simply unrealistic and improbable, and characters could still live through attacks that would render any real life person hospitalized for quite some time. That's the point I'm trying to make. The world of your game, regardless of genre, needs to be survivable and have plenty of opportunities to be a hero, or be challenged within a acceptable level. It seems like more and more GMs are taking this "me versus the players" approach to the games, and regardless of what you may think, I believe this is a terrible approach.
GMing--game mastering--is not about you lording over the players, monologuing for hours on end, and/or trying to kill the players' characters at every turn. It is about revealing the world to players, making rules decisions, and being a part of the group. I've played with GMs that completely lost sight of one or more of those things, and it was a horrible experience in every case. I wanted nothing more than to immediately leave. In a couple cases, I actually did. GMs are really a lot like teachers, and there is a specific skillset required to be a good GM, much like being a good teacher. Skill number one: leadership. Skill number two: communication. Skill number three: empathy. After that are additional skills such as critical thinking, good memory, creativity, etc. But those first three are critical to the success of any game/group. You are effectively the leader of the group, but as a leader you don't bark out orders, you "lead" the group. You help them make decisions, guide them to conclusions, and make judgment calls. But you do all this by communicating clearly and empathizing with the players. Give them outs for poor decisions from time to time. Never take a player's suggestion if it goes against your gut, or your plans for the story. Listen to the suggestion and shelve it for later as a possible idea for a plot line. And when it comes to the rules (and you can find this in practically every system written) they are suggestions for play. The are not etched in stone and if the story would be better served by ignoring a rule this go around because the story would be better, do just that. But also be fair and open. Tell the players that you are ignoring that rule for sake of the story. And this next part is critical, only do that for the players. The NPCs (non player characters that the GM controls) should never be allowed to break the rules. The players have a set reality of rules that they are assuming everyone has to play by, and if you get willy-nilly with those rules for the NPCs, the players will lose their suspension of disbelief and thus the fun quotient will drop. Yes, this means that the players will "win" more often, but that's the point--players are the protagonists of their combined story. Who wants to read about the heroes of the story dying? It simply isn't fun, and fun is what gaming is all about.
So in conclusion, the GM's job is a big one. You have to juggle a lot of stuff at once. And it isn't easy. It takes time to master the skills required, and some never even do that. Not everyone can be a GM either. There seems to be this feeling in the gaming society that anyone can be a GM, and while I can agree with that to a point, I have to define it a bit further, anyone can be a GM, but only certain people can be great GMs. I've played with many game designers and publishers over the years and surprisingly, a lot of them are not very good GMs. They have the imagination, creativity, and rules knowledge, but they lack the three primary skills of leadership, communication, and empathy. Many of them I've found to be in the camp of "kill as many characters as I can." That is typically only fun for one person, the GM. Gaming is all about creating heroes, hopefully epic heroes that will become legends in time. How could that happen if the GM seeks to kill them at every turn? Don't get me wrong though, challenge is a major part of the game play. The players need to be challenged, they need to fear for their characters' lives, but at the same time the GM should be looking to making these challenges exciting, but survivable. Now if a player just goes and does something that is beyond dumb because they think it would be funny and they know it will result in their character's death, I say they kind of deserve it. But if they they just made a bad judgement call and they were solidly in character, and felt there was a chance, make it a learning experience and let there be consequences other than death. Ultimately, your job as GM is to help the players tell a story of heroic endeavors and guide them through the world making memories that will last a lifetime.
PS: There are a lot of tools that GMs can use these days, but I would recommend just starting with the basics: paper, pencils, and dice alone. Once you get the knack of GMing with these simple tools, you can start adding additional "tools" such as miniatures, tokens, maps, electronic devices, etc. Just remember that very little can beat the theater of the mind. But if you have players that struggle with visualizing, than definitely add those simple tools as soon as possible because you are an empathetic GM and want to help the players as much as you can.
This nine minute video really sums up what I want out of any game I play or GM, and is the pinnacle of what gaming is all about for me. If you haven't ever seen this, or even if you have, please do yourself a favor and watch it, and when it is done, ask yourself if you would like to achieve this as a player, or have this be your story as a GM, and as a GM what will you do to make it a reality.
As for a great resource to improve your GMing skills, find great ideas to try, as well as tools you might find useful, I strongly recommend this one: https://roleplayingtips.com/ Note that there is a link to the blog at the bottom, and there is also a great newsletter that you can subscribe to that delivers content right to your inbox.
I've been playing RPGs since my first foray into AD&D in 1980. A childhood friend of mine and his brother bought the three core books and we decided to give it a go. It was relatively easy to become a DM back then--buy a module (a pre-written adventure), read it, and then take the players along for a ride through the module. The module had all the text that described the scene, had the monsters that would be encountered during said adventure, and the treasure that would be doled out once the monsters were slain. And as young kids, we didn't have all the weight of reality sitting on our shoulders. There was little effort required to suspend disbelief. We just got in to the story and went along for the ride. We joked, we ate, we socialized. It was all about improving our characters to become masters of the world, and for the GM it was all about telling the story and finally sharing the secrets and surprises that the players had yet to uncover. For everyone it was about hanging with friends, socializing, and building memories that would be shared for decades. Unfortunately, so much of that has been lost over the last couple decades, and gaming has morphed into a "me, the GM, versus you, the players." This is not conducive to shared fun or fond memories. We've lost sight of the core of gaming, acceptance of fantasy, and especially what a GM's job is.
Socializing, that's the core of gaming. If you can't enjoy hanging out as a group just talking, you probably shouldn't be gaming together. This is the first key point, and so critical to gaming in general. I've played with many groups over the years, both face-to-face and online, and the majority of those groups were not fun to be a part of. It could have been something minor like one of the players just constantly cracking unfunny jokes, something a bit more serious like favoritism among the established friends, to something pretty major such as constant arguing about everything that everyone was doing wrong. I saw it from GMs as well as players. Any injection of poison into the group will result in the dissolving of the group, or at the very least splintering, as irritated players leave the group. Sadly, this poison is almost always the fault of the GM, in the majority of the groups that I joined and then quickly left. (Note: I did not leave all the groups because of that, some I simply couldn't play with due to real life issues getting in the way, especially as I got older, so don't assume a player's departure is do to "poison." Communication is critical here.) As I just mentioned, communication is critical in any group. Everyone needs to be a respected member of the group and treated as an equal. If the group cannot communicate and be honest and open with one another that tends to indicate an underlying problem and the group should either work on fixing it, or breaking up before feelings are really hurt. This is one of the first jobs of the GM--communication. Not just taking the group on the adventure, but also making sure that everyone is treated fairly and equally. Every player should be given an opportunity to give input, and to make mistakes. If a player makes a mistake, don't ridicule the player - a little friendly ribbing is fine, but make it and keep it friendly. The GM is telling a story that is typically only faintly based in reality, after all who wants to play the game commuting to work and doing business after a week of really doing just that. Games are meant to be fantastic, fun, and frivolous.
Fantasy, not swords and sorcery, but the opposite of reality, is what the gaming worlds are set in regardless of the genre. It could be a gritty realistic mission set in modern day, trying to stop some evil corporation from controlling the minds of the populace, but it is still fantasy, and should be treated as such. I feel like the older we get the more we lose sight of the ability to suspend disbelief and we keep demanding more and more realism in our games, and I think this is a very wrong approach to take. Sure, you can go for a high level of reality, but if the players aren't larger than life heroes capable of extraordinary feats, what's the point? One of my favorite systems in my teen years was Aftermath, a game set in a post-apocalyptic world. The system is incredibly crunchy (high level of realism), and characters can die a million ways to Tuesday, but ultimately it was still fantasy. There were still elements of the game that were simply unrealistic and improbable, and characters could still live through attacks that would render any real life person hospitalized for quite some time. That's the point I'm trying to make. The world of your game, regardless of genre, needs to be survivable and have plenty of opportunities to be a hero, or be challenged within a acceptable level. It seems like more and more GMs are taking this "me versus the players" approach to the games, and regardless of what you may think, I believe this is a terrible approach.
GMing--game mastering--is not about you lording over the players, monologuing for hours on end, and/or trying to kill the players' characters at every turn. It is about revealing the world to players, making rules decisions, and being a part of the group. I've played with GMs that completely lost sight of one or more of those things, and it was a horrible experience in every case. I wanted nothing more than to immediately leave. In a couple cases, I actually did. GMs are really a lot like teachers, and there is a specific skillset required to be a good GM, much like being a good teacher. Skill number one: leadership. Skill number two: communication. Skill number three: empathy. After that are additional skills such as critical thinking, good memory, creativity, etc. But those first three are critical to the success of any game/group. You are effectively the leader of the group, but as a leader you don't bark out orders, you "lead" the group. You help them make decisions, guide them to conclusions, and make judgment calls. But you do all this by communicating clearly and empathizing with the players. Give them outs for poor decisions from time to time. Never take a player's suggestion if it goes against your gut, or your plans for the story. Listen to the suggestion and shelve it for later as a possible idea for a plot line. And when it comes to the rules (and you can find this in practically every system written) they are suggestions for play. The are not etched in stone and if the story would be better served by ignoring a rule this go around because the story would be better, do just that. But also be fair and open. Tell the players that you are ignoring that rule for sake of the story. And this next part is critical, only do that for the players. The NPCs (non player characters that the GM controls) should never be allowed to break the rules. The players have a set reality of rules that they are assuming everyone has to play by, and if you get willy-nilly with those rules for the NPCs, the players will lose their suspension of disbelief and thus the fun quotient will drop. Yes, this means that the players will "win" more often, but that's the point--players are the protagonists of their combined story. Who wants to read about the heroes of the story dying? It simply isn't fun, and fun is what gaming is all about.
So in conclusion, the GM's job is a big one. You have to juggle a lot of stuff at once. And it isn't easy. It takes time to master the skills required, and some never even do that. Not everyone can be a GM either. There seems to be this feeling in the gaming society that anyone can be a GM, and while I can agree with that to a point, I have to define it a bit further, anyone can be a GM, but only certain people can be great GMs. I've played with many game designers and publishers over the years and surprisingly, a lot of them are not very good GMs. They have the imagination, creativity, and rules knowledge, but they lack the three primary skills of leadership, communication, and empathy. Many of them I've found to be in the camp of "kill as many characters as I can." That is typically only fun for one person, the GM. Gaming is all about creating heroes, hopefully epic heroes that will become legends in time. How could that happen if the GM seeks to kill them at every turn? Don't get me wrong though, challenge is a major part of the game play. The players need to be challenged, they need to fear for their characters' lives, but at the same time the GM should be looking to making these challenges exciting, but survivable. Now if a player just goes and does something that is beyond dumb because they think it would be funny and they know it will result in their character's death, I say they kind of deserve it. But if they they just made a bad judgement call and they were solidly in character, and felt there was a chance, make it a learning experience and let there be consequences other than death. Ultimately, your job as GM is to help the players tell a story of heroic endeavors and guide them through the world making memories that will last a lifetime.
PS: There are a lot of tools that GMs can use these days, but I would recommend just starting with the basics: paper, pencils, and dice alone. Once you get the knack of GMing with these simple tools, you can start adding additional "tools" such as miniatures, tokens, maps, electronic devices, etc. Just remember that very little can beat the theater of the mind. But if you have players that struggle with visualizing, than definitely add those simple tools as soon as possible because you are an empathetic GM and want to help the players as much as you can.
This nine minute video really sums up what I want out of any game I play or GM, and is the pinnacle of what gaming is all about for me. If you haven't ever seen this, or even if you have, please do yourself a favor and watch it, and when it is done, ask yourself if you would like to achieve this as a player, or have this be your story as a GM, and as a GM what will you do to make it a reality.
As for a great resource to improve your GMing skills, find great ideas to try, as well as tools you might find useful, I strongly recommend this one: https://roleplayingtips.com/ Note that there is a link to the blog at the bottom, and there is also a great newsletter that you can subscribe to that delivers content right to your inbox.
Thursday, August 17, 2017
Uber Las Vegas
I recently posted about how Uber is a double-edged sword, but I have to say my Uber experiences in Las Vegas have been pretty good. The longest I've had to wait for an Uber has been 8 minutes, and every driver has been personable and helpful. I got great suggestions for restaurants and things to do.
One of my Uber drivers was Westley Stevens--apparently he and Lionel Richie had a bet going about who could earn the most while driving for Uber, or something. I think we was just trying to pay the bills. Regardless, he was quite entertaining and had a fun story to tell.
I had recommendations for Casa Don Juan where I had the chicken mole, and another recommendation for The Cornish Pasty Co where I had a pepper steak pasty. I strongly recommend both restaurants to anyone visiting Las Vegas.
One of my Uber drivers was Westley Stevens--apparently he and Lionel Richie had a bet going about who could earn the most while driving for Uber, or something. I think we was just trying to pay the bills. Regardless, he was quite entertaining and had a fun story to tell.
I had recommendations for Casa Don Juan where I had the chicken mole, and another recommendation for The Cornish Pasty Co where I had a pepper steak pasty. I strongly recommend both restaurants to anyone visiting Las Vegas.
And I definitely learned that I do not need to drive in Vegas with the convenience of Uber. And because everything is so close to the strip, most rides are less than $10, and even cheaper if you go with the Uber Pool option. The Pool option also has a high probability of meeting some fun people as well. I met a couple from Arizona that were really enjoying their time in Vegas and just happy as all get out. Today I shared a ride with a couple young women that were staying at my same hotel and were obviously enjoying their time in Vegas--interestingly they were returning from the grocery store with a couple shopping bags of groceries because they didn't want to go out to eat at restaurants. And I shared a ride with a guy that was there to see his son who played football for the University of Nevada and who was being recruited for the NFL.
It is amazing how much people can tell you about themselves in a short 10 minute ride when they are happy and willing to share. Surprisingly none of these people were on their phones during the rides preferring to chat with a complete stranger instead. Almost makes me think driving for Uber could be a lot of fun, at least in Vegas.
Sunday, August 13, 2017
My Travel Kit
One of the common questions I get asked when I'm at a customer and the discussion of travel comes up is, "So, what are your favorite gadgets to travel with and why?" My kit started off based on fantastic suggestions from my friend Nick who also travels a lot for work. I've refined things over the years and what I carry now are all essentials, and as light weight as I can pull off.
Let's take a closer look and break it all down.
Starting in the top left and going right and then down:
External Hard Drive - This is a 1 TB USB external drive that serves a duel purpose--large file transfers and stores my music, books, and video library. You'll notice that it is in a hard shell case as well. After replacing my previous external drive, I really took a look at it and saw how banged up it was, and decided that a case would be a good idea for my new drive.
5 Port USB Charging Hub - This is my newest addition, and has proven essential for bulk charging tasks of all my gadgets. Unfortunately, it isn't a true USB hub so I can't use it for connecting devices to my laptop. But it does have the exact number of ports I need to charge up everything at once. It will come in very handy on my next two week trip. If I were to replace this, I would try to find one that is also a connectivity hub because there are occasions when I connect at least four devices to my laptop at once.
6x8" Cocoon Organizer - When you have a lot of cables and little gadgets, you don't really want them rattling around in your bag, so this elastic mesh organizer is the perfect solution. The elastic bands make a web of varying lengths and sizes allowing you to find the perfect position for whatever you need to hold in place.
Various Cables - Just all the cables I have to haul around.
Bose Noise Cancelling Headphones - These would be the most expensive item in my bag other than my laptop. They are not cheap, but man do they live up to their reputation. These are essential for blocking out noise on flights and for listening to that movie or tunes that are helping the time fly by. I prefer the ear buds rather than the over-the-ear model because they are significantly lighter, easier to tote around, and can be easily thrown in a pocket when you need to run.
Hand Sanitizer - I work in the healthcare industry so this has become something I'm always aware of. It has a holder that hooks on to backpack making it always accessible whether I'm on the plane, or at a customer site. I actually buy a large bottle of it and use that to fill the small bottle. Saves on the landfill and the pocket book.
Towel - Yup. That's a towel. I actually travel with two of them. The small one you see here and a larger one that can also serve as a small ground cover or a bath towel. The larger one is stored in my rollaboard. This is a super absorbent towel kind of similar to the famous "Sham Wow" towel. It has various uses--go read Hitchhiker's Guide if you don't know why towels are so important. ;)
Multiport Video Adapter - As a technical trainer, I run into just about every type of video setup you can imagine so this adapter is essential allowing me to connect to just about every type of video connector I could run into.
Google Chromecast - When I want to watch Netflix, videos in my library, or have a customer that doesn't have the necessary cable for me to connect to, this things makes it all more enjoyable and easier to deal with. Most TVs in modern hotels have HDMI connections and a USB port or plug nearby. This is the Ultra model which allows for both USB or outlet power options.
Miniature Gripping Tripod - This doesn't get used all the time, but comes in handy when I need a steady shot, want to take a selfie at distance or even serves as a phone stand for watching the screen. The legs are flexible and can be positioned in all sorts of ways.
Microsoft Arc Mouse - I love this mouse! It lays flat until you need to use it. Then you simply snap it into an arc and it turns on. Super light weight, easy to transport, and can be used on any surface. It uses a Bluetooth dongle instead of a wire which is also nice.
Gorilla Gadgets Battery Pack - This bad boy packs 16800mAh, and has two output ports. It is also one of the heavier gadgets I have, but it now lives in my rollaboard attached to the external USB connection giving me a convenient charging option rather than depending on an outlet to be open.
Belkin Power Adapter - This is my most used and second favorite gadget. It has three standard AC outlets and two USB outlets. I am always running into situations where this comes in incredibly handy whether it is a customer site, or the departure gate at the airport. That last situation has earned me some friends when people were looking for a plug to charge up their phone but all the plugs are filled. I swoop in and offer to extend that one plug to allow four more people to charge their devices.
Wi-Fi AC750 Portable Router and Charger - This is my favorite gadget. This was actually given to me by my work's IT staff. I can not rave about this router enough. I use it during my training classes allowing up to 15 people to connect to my laptop's VMs. I also use it in the hotel room to give all my gadget's a single connection to use, rather than logging in from each device, including my Chromecast, which solves the problem of not being able to use a Chromecast in a hotel room. Plus this thing has a built-in DLNA server so I can plug my external hard drive into it and stream videos and music directly off it. Oh, and it is also a rechargeable battery for my devices should I need another one. Did I mention how much I like this thing?
Verizon 4GLTE JetPack Mi-Fi - Another work issued gadget. This thing is my safety net for connectivity. You have no idea how many hospitals have horrible WiFi networks. This also provides a safer connection than the typical public network you find in airports.
ASUS Nexus 7 Tablet - I use this tablet primarily for consuming media--books, videos, music--when flying. It is big enough to watch a movie on comfortably even in cramped airplane seats, but small enough that it can be slipped into a back pocket. I also play an occasional game on it.
Tripp-Lite Keyspan Projector Remote - (Not pictured) This isn't so much a travel gadget, but it is my "tool of the trade." As a professional trainer, I need a good remote for interacting with PowerPoint and my computer from a distance. This remote has an integrated mouse, presentation buttons, volume control, and laser pointer. Basically, it has everything short of a keyboard integrated into it.
So that's it. There are a other things I carry that aren't gadgets, but are quality of life things for the hotel room, work, etc. like sleep mask, PostIt notes (that's another post for another day), and water bottle.
I hope this post helps you plan for your own tech filled trips, and if you have any suggestions that you've found useful, please share in the comments below.
Let's take a closer look and break it all down.
Starting in the top left and going right and then down:
External Hard Drive - This is a 1 TB USB external drive that serves a duel purpose--large file transfers and stores my music, books, and video library. You'll notice that it is in a hard shell case as well. After replacing my previous external drive, I really took a look at it and saw how banged up it was, and decided that a case would be a good idea for my new drive.
5 Port USB Charging Hub - This is my newest addition, and has proven essential for bulk charging tasks of all my gadgets. Unfortunately, it isn't a true USB hub so I can't use it for connecting devices to my laptop. But it does have the exact number of ports I need to charge up everything at once. It will come in very handy on my next two week trip. If I were to replace this, I would try to find one that is also a connectivity hub because there are occasions when I connect at least four devices to my laptop at once.
6x8" Cocoon Organizer - When you have a lot of cables and little gadgets, you don't really want them rattling around in your bag, so this elastic mesh organizer is the perfect solution. The elastic bands make a web of varying lengths and sizes allowing you to find the perfect position for whatever you need to hold in place.
Various Cables - Just all the cables I have to haul around.
Bose Noise Cancelling Headphones - These would be the most expensive item in my bag other than my laptop. They are not cheap, but man do they live up to their reputation. These are essential for blocking out noise on flights and for listening to that movie or tunes that are helping the time fly by. I prefer the ear buds rather than the over-the-ear model because they are significantly lighter, easier to tote around, and can be easily thrown in a pocket when you need to run.
Hand Sanitizer - I work in the healthcare industry so this has become something I'm always aware of. It has a holder that hooks on to backpack making it always accessible whether I'm on the plane, or at a customer site. I actually buy a large bottle of it and use that to fill the small bottle. Saves on the landfill and the pocket book.
Towel - Yup. That's a towel. I actually travel with two of them. The small one you see here and a larger one that can also serve as a small ground cover or a bath towel. The larger one is stored in my rollaboard. This is a super absorbent towel kind of similar to the famous "Sham Wow" towel. It has various uses--go read Hitchhiker's Guide if you don't know why towels are so important. ;)
Multiport Video Adapter - As a technical trainer, I run into just about every type of video setup you can imagine so this adapter is essential allowing me to connect to just about every type of video connector I could run into.
Google Chromecast - When I want to watch Netflix, videos in my library, or have a customer that doesn't have the necessary cable for me to connect to, this things makes it all more enjoyable and easier to deal with. Most TVs in modern hotels have HDMI connections and a USB port or plug nearby. This is the Ultra model which allows for both USB or outlet power options.
Miniature Gripping Tripod - This doesn't get used all the time, but comes in handy when I need a steady shot, want to take a selfie at distance or even serves as a phone stand for watching the screen. The legs are flexible and can be positioned in all sorts of ways.
Microsoft Arc Mouse - I love this mouse! It lays flat until you need to use it. Then you simply snap it into an arc and it turns on. Super light weight, easy to transport, and can be used on any surface. It uses a Bluetooth dongle instead of a wire which is also nice.
Gorilla Gadgets Battery Pack - This bad boy packs 16800mAh, and has two output ports. It is also one of the heavier gadgets I have, but it now lives in my rollaboard attached to the external USB connection giving me a convenient charging option rather than depending on an outlet to be open.
Belkin Power Adapter - This is my most used and second favorite gadget. It has three standard AC outlets and two USB outlets. I am always running into situations where this comes in incredibly handy whether it is a customer site, or the departure gate at the airport. That last situation has earned me some friends when people were looking for a plug to charge up their phone but all the plugs are filled. I swoop in and offer to extend that one plug to allow four more people to charge their devices.
Wi-Fi AC750 Portable Router and Charger - This is my favorite gadget. This was actually given to me by my work's IT staff. I can not rave about this router enough. I use it during my training classes allowing up to 15 people to connect to my laptop's VMs. I also use it in the hotel room to give all my gadget's a single connection to use, rather than logging in from each device, including my Chromecast, which solves the problem of not being able to use a Chromecast in a hotel room. Plus this thing has a built-in DLNA server so I can plug my external hard drive into it and stream videos and music directly off it. Oh, and it is also a rechargeable battery for my devices should I need another one. Did I mention how much I like this thing?
Verizon 4GLTE JetPack Mi-Fi - Another work issued gadget. This thing is my safety net for connectivity. You have no idea how many hospitals have horrible WiFi networks. This also provides a safer connection than the typical public network you find in airports.
ASUS Nexus 7 Tablet - I use this tablet primarily for consuming media--books, videos, music--when flying. It is big enough to watch a movie on comfortably even in cramped airplane seats, but small enough that it can be slipped into a back pocket. I also play an occasional game on it.
Tripp-Lite Keyspan Projector Remote - (Not pictured) This isn't so much a travel gadget, but it is my "tool of the trade." As a professional trainer, I need a good remote for interacting with PowerPoint and my computer from a distance. This remote has an integrated mouse, presentation buttons, volume control, and laser pointer. Basically, it has everything short of a keyboard integrated into it.
So that's it. There are a other things I carry that aren't gadgets, but are quality of life things for the hotel room, work, etc. like sleep mask, PostIt notes (that's another post for another day), and water bottle.
I hope this post helps you plan for your own tech filled trips, and if you have any suggestions that you've found useful, please share in the comments below.
Monday, August 7, 2017
Deep Sea Fishing
Last week while in Massachusetts I went on a team building adventure--deep sea fishing. I've fished in rivers and lakes, but this was my first time out at sea, and admittedly, it wasn't that far from shore, but technically it was still the Atlantic Ocean. I was a little concerned about sea sickness, even though historically I typically don't get motion sick, but since it was my first time I had my concern and I didn't want to be the guy that fed the fish (that honor did go to one of my co-workers who shall remain nameless),. Thankfully I didn't get sick at all, which made the trip even better.
I definitely recommend that you should take a charter some time and experience the fun that is deep sea fishing. By the end of the day I had caught four different kinds of fish--red fish, cod, haddock, and a sand shark.
I definitely recommend that you should take a charter some time and experience the fun that is deep sea fishing. By the end of the day I had caught four different kinds of fish--red fish, cod, haddock, and a sand shark.
The fish on the left was the first fish I caught and was the first for the trip. It is a red fish, and the bulging eyes are caused by the pressure differential. Apparently this fish is very pressure sensitive, and died on the way up. The fin on its back is actually venomous and if it sticks you, it feels like a bee sting. The fish I'm holding up is a cod, which unfortunately we couldn't keep due to some fishing law, so I had to toss it back. We did get to keep all the haddock we caught, but the sand sharks we caught had to be thrown back. By the way, sand sharks have a very sharp barb on the rear fin that faces forward and if you are a foolish predator and try to grab it from behind, the barb sticks in you and delivers some serious venom. Yet another reason the ocean will kill you.
The best thing about the trip was just being out in the open water away from people and the city, and listening to the waves, sea gulls, and the occasional boat. I kept my phone in the cabin while fishing, and only had it out during the trip out to the water. Here are some of the scenic shots I took while leaving port.
During the trip, we saw another "party" fishing boat, and the first mate on our boat talked about how those boats leave people mad, generally speaking. One of my coworkers had experienced one, and agreed. Apparently, fishing lines are constantly getting tangled and the time spent fishing is minimal. That said, aim for the smaller more private boats.
Once the trip was over we returned to the marina and took our fillets to the marina restaurant where they cooked them up and added some sides and drinks.
It made for the freshest fish and chips lunch I've ever had. Tasted great! Oh, and in case you are curious where we went, here's a Google Map of the trip. Disregard all the land connections. It kept trying to connect to non GPS locations. We chartered the Karen Lynn, and I want to give a special shout out to Collin and Bryce who made the trip a blast.
Saturday, August 5, 2017
Are You Ready Player One?
Just finished reading Ready Player One, and if you are/were a geek child/teen of the 80s, this book is absolutely for you! There is also a movie adaptation coming out for it. More on that later.
The book is cover to cover references to geek culture from the late 20th century, and if you played RPGs /video games, and watched sci-fi/fantasy movies and/or Saturday morning cartoons, or read manga/watched anime, or enjoyed Monte Python, or anything related to any of that stuff, this book will keep you reading. I read it on the plane ride to and from Boston last week, so it was roughly a 14 hour read.
As you might be able to tell from that last paragraph, it touches on a lot of different things from that time, and has a little something for every geek out there. I won't spoil anything beyond what you can read on the back cover:
It takes place in 2044/45 mostly inside a virtual utopia known as the OASIS (it's an acronym, read the book to find out what it stands for), and the protagonist's quest to find the creator's hidden secret within the universe of the Oasis.
That description really doesn't do it justice, but trust me, you'll love it.
And there is a movie that is currently in post-production. You can watch the trailer here:
I watch the trailer, and there are really only a couple scenes and a handful of elements that I recognize from the book, which makes me a little sad. But Steven Spielberg is directing it, so I'm holding out a little hope that it will be well received. This article does make some some good arguments regarding it needing to be different/better than the book, but my primary fear is that it will lose its heart and core story in that transformation. But we'll have to wait and see.
The book is cover to cover references to geek culture from the late 20th century, and if you played RPGs /video games, and watched sci-fi/fantasy movies and/or Saturday morning cartoons, or read manga/watched anime, or enjoyed Monte Python, or anything related to any of that stuff, this book will keep you reading. I read it on the plane ride to and from Boston last week, so it was roughly a 14 hour read.
As you might be able to tell from that last paragraph, it touches on a lot of different things from that time, and has a little something for every geek out there. I won't spoil anything beyond what you can read on the back cover:
It takes place in 2044/45 mostly inside a virtual utopia known as the OASIS (it's an acronym, read the book to find out what it stands for), and the protagonist's quest to find the creator's hidden secret within the universe of the Oasis.
That description really doesn't do it justice, but trust me, you'll love it.
And there is a movie that is currently in post-production. You can watch the trailer here:
I watch the trailer, and there are really only a couple scenes and a handful of elements that I recognize from the book, which makes me a little sad. But Steven Spielberg is directing it, so I'm holding out a little hope that it will be well received. This article does make some some good arguments regarding it needing to be different/better than the book, but my primary fear is that it will lose its heart and core story in that transformation. But we'll have to wait and see.
Subscribe to:
Posts (Atom)